Generating Public Private Rsa Key Pair Ubuntu
- Generating Public Private Rsa Key Pair Ubuntu Free
- Generating Public Private Rsa Key Pair Ubuntu Download
I want to generate GnuPG public private key pairs. I have gpg and not gpg2 installed.So I went to terminal and did. Gpg -gen-key output: Please select what kind of key you want: (1) RSA and RSA (default) (2) DSA and Elgamal (3) DSA (sign only) (4) RSA (sign only). Jul 30, 2015 RSA is the only recommended choice for new keys, so this guide uses 'RSA key' and 'SSH key' interchangeably. Key-based authentication uses two keys, one 'public' key that anyone is allowed to see, and another 'private' key that only the owner is allowed to see. Apr 02, 2019 As a matter of fact, generating a key pair offers users two lengthy strings of characters corresponding to a public as well as a private key. Users can, thus, place the public key on any server, and subsequently, unlock the same by connecting to it with a client that already possesses the private key.
This tutorial series will teach you how to use GPG in Linux terminal. I will not tell you a bunch of theory to overwhelm you. Instead, I show you quick and dirty examples to get you started, and explain the basic theory along the way.
This is part 1 of this series. At the end of this post, you should be able to generate your own public/private keypair and a revocation certificate. This certificate is used to revoke your public/private keypair when your private key is compromised or you forget the passphrase for your private key.
GPG can be used for encryption and for signing. This software is pre-installed on most Linux distributions. Currently the stable version is GPG 2.0. I’m using the modern version GPG 2.2 on Arch Linux.
Check Your GPG Version
First Let’s check out the version of GPG on your system and some interesting tidbits. Run the following command.
As you can see, I’m using GPG 2.2.8, which is the latest version. Git generate private key windows. We also know that the configuration directory is ~/.gnupg, which will hold our public/private key files. The default option file is ~/.gnupg/gpg.conf and ~/.gnupg/dirmngr.conf. It also tells us what algorithms are supported.
If you look closely, you can see that the insecure hash algorithm SHA1 is still supported in version 2.2.8 SHA1 is obsolete and you don’t want to use it to generate signature.
Create Your Public/Private Key Pair and Revocation Certificate
Use gpg --full-gen-key command to generate your key pair.
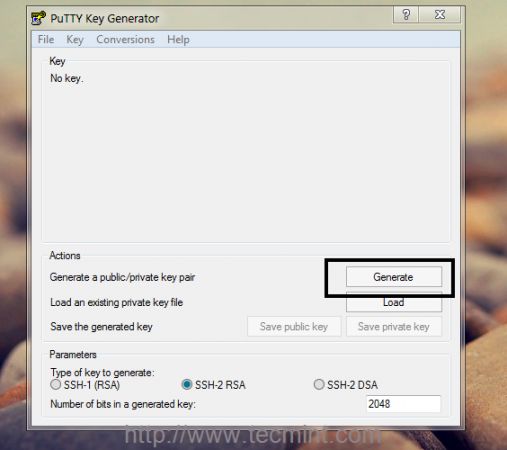
It asks you what kind of key you want. Notice there’re four options. The default is to create a RSA public/private key pair and also a RSA signing key. Let’s hit Enter to select the default.
Next it asks you the key length. The default is 2048 bits long. 1024 RSA key is obsolete. The longer 4096 RSA key will not provide more security than 2048 RSA key. So hit Enter to select the default.
280 slides free download mac. After that it asks you how long the key should be valid, 2 years is fine. You can always update the expiration time later on.
Now it asks you if it’s correct. Notice that the default is No. So press y then Enter to confirm it’s correct.
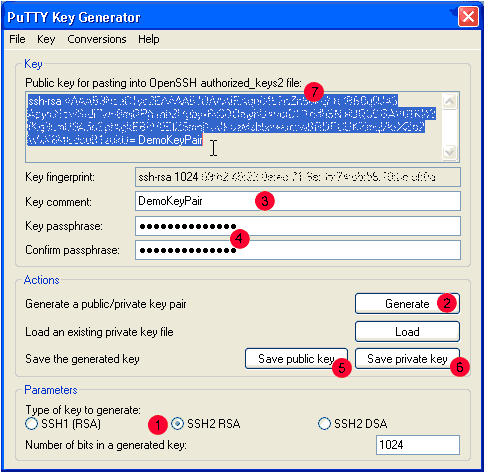
And now we need to provide some user identification information for the key. This is important because this information will be included in our key. It’s one way of indicating who is owner of this key. The email address is a unique identifier for a person. You can leave Comment blank.
Generating Public Private Rsa Key Pair Ubuntu Free
Select Okay.
Now it asks you to enter a passphrase to protect your private key. Enter a good and long passphrase and remember it. Because if you forget this passphrase, you won’t be able to unlock you private key.
Once you enter and confirm your passphrase. GPG will generate your keys.
It will take a while for GPG to generate your keys. So you can now do other stuff.
It took about 4 minutes on my system to generate my key pair.
This first line tells us that GPG created a unique identifier for public key. This unique identifier is in hex format. When someone wants to download you public key, they can refer to you public key via your email address or this hex value.
The third line tells us that GPG created a revocation certificate and its directory.Your should never share you private key with anyone.If you private key is compromised, you can use revocateion certificate to revoke your key. That means you tell the rest of the world that the old public key shall not be used any more.I suggest that you open this revocation certificate with your text editor to see what’s inside there.
Let’s look at the last three lines. They tell us the public key is 2048 bits using RSA algorithm. The public key ID 4F0BDACC matchs the last 8 bits of key fingerprint. The key fingerprint is a hash of your public key.
It also lists our user ID information: your name and your email address. And it also indicates the subkey which is 2048 bits using RSA algorithm and the unique identifier of the subkey.
Now you can find that there are two files created under ~/.gnupg/private-keys-v1.d/ directory. These two files are binary files with .key extension.
Export Your Public Key
Others need your public key to send encrypted message to you and only your private key can decrypt it. Use the following command to export your public key. --armor option means that the output is ASCII armored. The default is to create the binary OpenPGP format. user-id is your email address.
The exported public key is written to pubkey.asc file.
Export Your Private Key
Issue the following command to export your private key.
The exported key is written to privkey.asc file.
Protect Your Private Key and Revocation Certificate
Your private key should be kept in a safe place, like an encrypted flash drive. Treat it like your house key. Only you can have it and don’t lose it. And you must remember your passphrase, otherwise you can’t unlock your private key.
You should also protect your revocation certificate. If others have your revocation certificate, they can immediately revoke your public/private keypair and generate a fake public/priavte keypair.
In part 2 we will look at how to encrypt message with your public key and how to decrypt it with your private key. Take care!
Generating Public Private Rsa Key Pair Ubuntu Download
With a secure shell (SSH) key pair, you can create virtual machines (VMs) in Azure that use SSH keys for authentication, eliminating the need for passwords to sign in. This article shows you how to quickly generate and use an SSH public-private key file pair for Linux VMs. You can complete these steps with the Azure Cloud Shell, a macOS or Linux host, the Windows Subsystem for Linux, and other tools that support OpenSSH.
Note
VMs created using SSH keys are by default configured with passwords disabled, which greatly increases the difficulty of brute-force guessing attacks.
For more background and examples, see Detailed steps to create SSH key pairs.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Supported SSH key formats
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
Create an SSH key pair
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the ~/.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten.
The following command creates an SSH key pair using RSA encryption and a bit length of 4096:
If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the --generate-ssh-keys option. The key files are stored in the ~/.ssh directory unless specified otherwise with the --ssh-dest-key-path option. The --generate-ssh-keys option will not overwrite existing key files, instead returning an error. In the following command, replace VMname and RGname with your own values:
Provide an SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods:
If you're not familiar with the format of an SSH public key, you can display your public key with the following cat command, replacing ~/.ssh/id_rsa.pub with the path and filename of your own public key file if needed:
A typical public key value looks like this example:
If you copy and paste the contents of the public key file to use in the Azure portal or a Resource Manager template, make sure you don't copy any trailing whitespace. To copy a public key in macOS, you can pipe the public key file to pbcopy. Similarly in Linux, you can pipe the public key file to programs such as xclip.
The public key that you place on your Linux VM in Azure is by default stored in ~/.ssh/id_rsa.pub, unless you specified a different location when you created the key pair. To use the Azure CLI 2.0 to create your VM with an existing public key, specify the value and optionally the location of this public key using the az vm create command with the --ssh-key-values option. In the following command, replace VMname, RGname, and keyFile with your own values:
If you want to use multiple SSH keys with your VM, you can enter them in a space-separated list, like this --ssh-key-values sshkey-desktop.pub sshkey-laptop.pub.
SSH into your VM
With the public key deployed on your Azure VM, and the private key on your local system, SSH into your VM using the IP address or DNS name of your VM. In the following command, replace azureuser and myvm.westus.cloudapp.azure.com with the administrator user name and the fully qualified domain name (or IP address):
If you specified a passphrase when you created your key pair, enter that passphrase when prompted during the login process. The VM is added to your ~/.ssh/known_hosts file, and you won't be asked to connect again until either the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
Next steps
For more information on working with SSH key pairs, see Detailed steps to create and manage SSH key pairs.
If you have difficulties with SSH connections to Azure VMs, see Troubleshoot SSH connections to an Azure Linux VM.