Generate Ssh Key For Users Linux
- Generate Ssh Key For Users Linux Windows 10
- Generate Ssh Key For Users Linux Windows 10
- Generate Ssh Key Linux Azure
- Mac Generate Ssh Key
- How To Generate Ssh Keys
Nov 10, 2011 How to Generate A Public/Private SSH Key Linux By Damien – Posted on Nov 10, 2011 Nov 18, 2011 in Linux If you are using SSH frequently to connect to a remote host, one of the way to secure the connection is to use a public/private SSH key so no password is transmitted over the network and it can prevent against brute force attack. Aug 19, 2019 Secure Shell (SSH) is an encrypted protocol used by Linux users to connect to their remote servers. Generally, there are two ways for clients to access their servers – using password based authentication or public key based authentication. Using SSH keys for authentication is highly recommended, as a safer alternative to passwords. I want to add a user to Red Hat Linux that will not use a password for logging in, but instead use a public key for ssh. This would be on the command line. Then create.ssh/authorizedkeys file in their home directory with their public key. Share improve this answer. Answered Jun 9 '17 at 22:32.
I want to add new user accounts that can connect to my Amazon Elastic Compute Cloud (Amazon EC2) Linux instance using SSH. How do I do that?
SSH keys are created using a key generation tool. The SSH command line tool suite includes a keygen tool. Most git hosting providers offer guides on how to create an SSH Key. Generate an SSH Key on Mac and Linux. Both OsX and Linux operating systems have comprehensive modern terminal applications that ship with the SSH suite installed. Users would be able to copy the public key into the authorizedkeys file of the new machine using the ssh-copy-id command. Given below is the prescribed format (strictly an example) for keying in the username and IP address, and must be replaced with actual system values. Aug 07, 2019. Adding your SSH key to the ssh-agent. Before adding a new SSH key to the ssh-agent to manage your keys, you should have checked for existing SSH keys and generated a new SSH key. When adding your SSH key to the agent, use the default macOS ssh-add command, and not an application installed by macports, homebrew, or some other external source.
Short Description
Every Amazon EC2 Linux instance launches with a default system user account with administrative access to the instance. If multiple users require access to the instance, it's a security best practice to use separate accounts for each user.
You can expedite these steps by using cloud-init and user data. For more information, see How can I give a user permissions to connect to my EC2 Linux instance using SSH?
Resolution
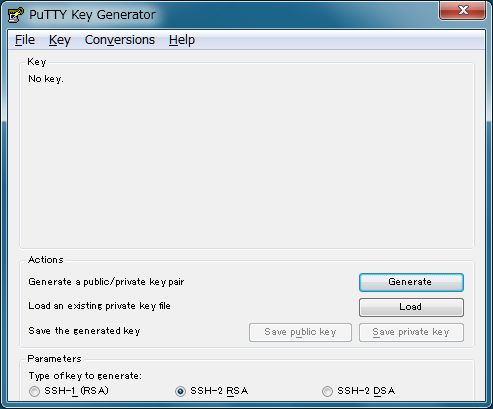
Create a key pair for the new user account
- Create a key pair, or use an existing one, for the new user.
- If you create your own key pair using the command line, follow the recommendations at create-key-pair or New-EC2KeyPair Cmdlet for key type and bit length.
- If you create your own key pair using a third-party tool, be sure that your key matches the guidelines at Importing Your Own Public Key to Amazon EC2.
Add a new user to the EC2 Linux instance
1. Connect to your Linux instance using SSH.
2. Use the adduser command to add a new user account to an EC2 instance (replace new_user with the new account name). The following example creates an associated group, home directory, and an entry in the /etc/passwd file of the instance:
Note: If you add the new_user to an Ubuntu instance, include the --disabled-password option to avoid adding a password to the new account:
3. Change the security context to the new_user account so that folders and files you create have the correct permissions:
Note: When you run the sudo su - new_user command, the name at the top of the command shell prompt changes to reflect the new user account context of your shell session.
4. Create a .ssh directory in the new_user home directory:
5. Use the chmod command to change the .ssh directory's permissions to 700. Changing the permissions restricts access so that only the new_user can read, write, or open the .ssh directory.
6. Use the touch command to create the authorized_keys file in the .ssh directory:
7. Use the chmod command to change the .ssh/authorized_keys file permissions to 600. Changing the file permissions restricts read or write access to the new_user.
Retrieve the public key for your key pair
Retrieve the public key for your key pair using the method that applies to your configuration:
Verify your key pair's fingerprint
After you import your own public key or retrieve the public key for your key pair, follow the steps at Verifying Your Key Pair's Fingerprint.
Update and verify the new user account credentials
After you retrieve the public key, use the command shell session that is running under the context of the new user account to confirm that you have permission to add the public key to the .ssh/authorized_keys file for this account:
1. Run the Linux cat command in append mode:
2. Paste the public key into the .ssh/authorized_keys file and then press Enter.
Note: For most Linux command line interfaces, the Ctrl+Shift+V key combination pastes the contents of the clipboard into the command line window. For the PuTTY command line interface, right-click to paste the contents of the clipboard into the PuTTY command line window.
3. Press and hold Ctrl+d to exit cat and return to the command line session prompt.
(Optional) Allow the new user to use sudo
Note: If you don't want to allow the new user to use sudo, proceed to Verify that the new user can use SSH to connect to the EC2 instance.
1. Use the passwd command to create a password for the new user:
Note: You're prompted to reenter the password. Enter the password a second time to confirm it.
2. Add the new user to the correct group.
For Amazon Linux, Amazon Linux 2, RHEL, and CentOS:
Use the usermod command to add the user to the wheel group.
For Ubuntu:
Use the usermod command to add the user to the sudo group.
Verify that the new user can use SSH to connect to the EC2 instance
1. Verify that you can connect to your EC2 instance when using ssh as the new_user by running the following command from a command line prompt on your local computer:
To connect to your EC2 Linux instance using SSH from Windows, follow the steps at Connecting to Your Linux Instance from Windows Using PuTTY.
2. After you connect to your instance as the new_user by using SSH, run the id command from the EC2 instance command line to view the user and group information created for the new_user account:
The id command returns information similar to the following:
3. Distribute the private key file to your new user.
Related Information
Anything we could improve?
Need more help?
Related Videos
 -->
-->With a secure shell (SSH) key pair, you can create virtual machines (VMs) in Azure that use SSH keys for authentication, eliminating the need for passwords to sign in. This article shows you how to quickly generate and use an SSH public-private key file pair for Linux VMs. You can complete these steps with the Azure Cloud Shell, a macOS or Linux host, the Windows Subsystem for Linux, and other tools that support OpenSSH.
Note
VMs created using SSH keys are by default configured with passwords disabled, which greatly increases the difficulty of brute-force guessing attacks.
Generate Ssh Key For Users Linux Windows 10
For more background and examples, see Detailed steps to create SSH key pairs.
For additional ways to generate and use SSH keys on a Windows computer, see How to use SSH keys with Windows on Azure.
Supported SSH key formats
Azure currently supports SSH protocol 2 (SSH-2) RSA public-private key pairs with a minimum length of 2048 bits. Other key formats such as ED25519 and ECDSA are not supported.
Generate Ssh Key For Users Linux Windows 10
Create an SSH key pair
Use the ssh-keygen command to generate SSH public and private key files. By default, these files are created in the ~/.ssh directory. You can specify a different location, and an optional password (passphrase) to access the private key file. If an SSH key pair with the same name exists in the given location, those files are overwritten.
The following command creates an SSH key pair using RSA encryption and a bit length of 4096:
If you use the Azure CLI to create your VM with the az vm create command, you can optionally generate SSH public and private key files using the --generate-ssh-keys option. The key files are stored in the ~/.ssh directory unless specified otherwise with the --ssh-dest-key-path option. The --generate-ssh-keys option will not overwrite existing key files, instead returning an error. In the following command, replace VMname and RGname with your own values:
Generate Ssh Key Linux Azure
Provide an SSH public key when deploying a VM
To create a Linux VM that uses SSH keys for authentication, specify your SSH public key when creating the VM using the Azure portal, Azure CLI, Azure Resource Manager templates, or other methods:
If you're not familiar with the format of an SSH public key, you can display your public key with the following cat command, replacing ~/.ssh/id_rsa.pub with the path and filename of your own public key file if needed:
A typical public key value looks like this example:
If you copy and paste the contents of the public key file to use in the Azure portal or a Resource Manager template, make sure you don't copy any trailing whitespace. To copy a public key in macOS, you can pipe the public key file to pbcopy. Similarly in Linux, you can pipe the public key file to programs such as xclip.
The public key that you place on your Linux VM in Azure is by default stored in ~/.ssh/id_rsa.pub, unless you specified a different location when you created the key pair. To use the Azure CLI 2.0 to create your VM with an existing public key, specify the value and optionally the location of this public key using the az vm create command with the --ssh-key-values option. In the following command, replace VMname, RGname, and keyFile with your own values:
If you want to use multiple SSH keys with your VM, you can enter them in a space-separated list, like this --ssh-key-values sshkey-desktop.pub sshkey-laptop.pub.
SSH into your VM
Mac Generate Ssh Key
With the public key deployed on your Azure VM, and the private key on your local system, SSH into your VM using the IP address or DNS name of your VM. In the following command, replace azureuser and myvm.westus.cloudapp.azure.com with the administrator user name and the fully qualified domain name (or IP address):
If you specified a passphrase when you created your key pair, enter that passphrase when prompted during the login process. /key-word-generator-based-on-my-website.html. The VM is added to your ~/.ssh/known_hosts file, and you won't be asked to connect again until either the public key on your Azure VM changes or the server name is removed from ~/.ssh/known_hosts.
If the VM is using the just-in-time access policy, you need to request access before you can connect to the VM. For more information about the just-in-time policy, see Manage virtual machine access using the just in time policy.
How To Generate Ssh Keys
Next steps
For more information on working with SSH key pairs, see Detailed steps to create and manage SSH key pairs.
If you have difficulties with SSH connections to Azure VMs, see Troubleshoot SSH connections to an Azure Linux VM.